PHP & JSP SQL Injection Remediations
Today We talk about PHP and JSP vulnerable code and how to solve quickly these problems.
Whenever an input is not monitored problems arise!
PHP:
This is a vulnerable php code; user inputs are inserted directly into the sql query: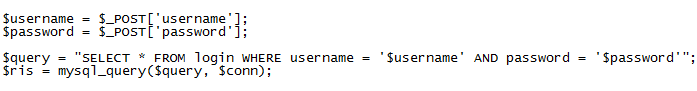
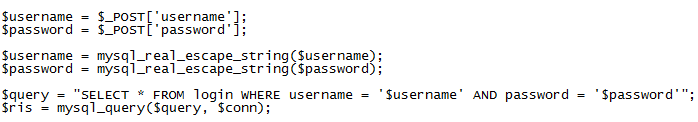
Using mysql_real_escape_string the problem is solved:
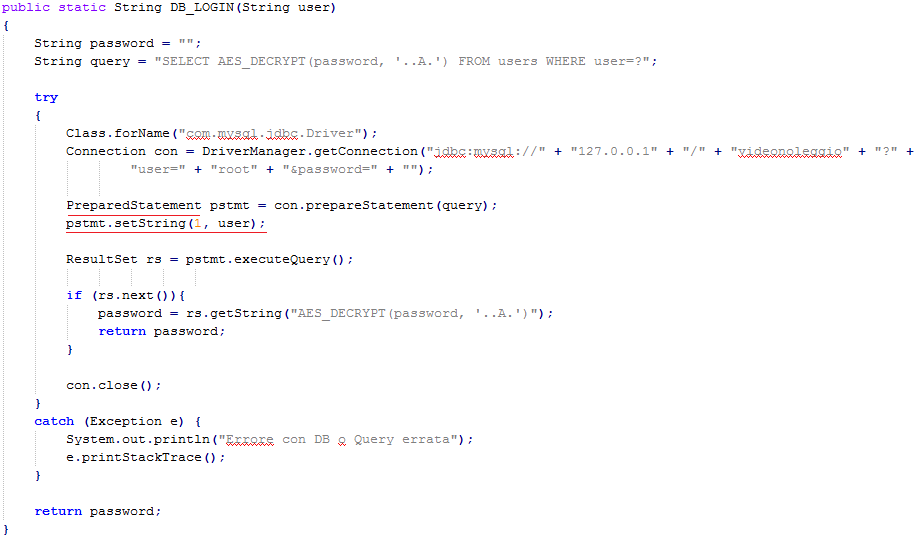
JSP:
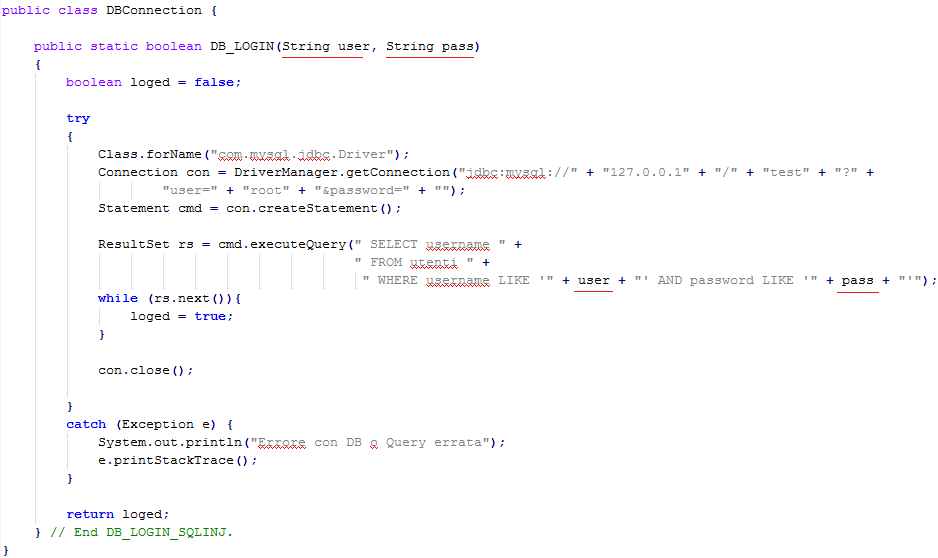
Here We have the page that gets the inputs and also the Java class that executes the query: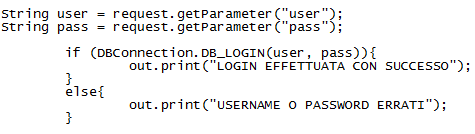
In this case the problem is solved with PreparedStatement:
Study hard and have fun :)